Bybit $1.5B Theft: Cold Wallet Controls Still Fail
When a third-party signing interface and privileged approvals get manipulated, offline storage becomes an assumption—not a guarantee.
By Aaron Gilmore — Intergalactic SEM Consultant (humans only so far).
Human-led, Automation-Enhanced. SEM-Artificium
QuickScan
“Cold” storage can still fail if the signing/approval workflow is compromised or deceived.
Treat high-value transfers and approvals as privileged operations (independent verification + logging).
Third-party tooling in your control plane must be governed like a critical vendor (requirements, monitoring, audit rights).
Pre-write and drill first-24-hour comms so technical containment and credibility move together.
For Who Primary audience: DoD/Federal Supply Chain Best for roles: Security leadership (CISO/CIO), Incident Response & Security Engineering, Contracting/Vendor Risk + Legal/Comms
What You’ll Get You will learn: Why “offline” controls can be defeated at the human + interface layer—and what that means for any high-value workflow.
You will be able to do: Identify and harden your highest-risk approval workflow using out-of-band verification, vendor control-plane governance, and rehearsed communications.
Time & Effort Read time: 7 minutes
Do time (optional): 30–60 minutes
Difficulty: Intermediate
Cold storage isn’t a guarantee if the signing/approval workflow can be manipulated.
Executive Snapshot
On or about February 21, 2025, cryptocurrency exchange Bybit reported a theft of approximately $1.5B in virtual assets after an attacker manipulated a routine transfer workflow involving an Ethereum cold wallet and a multi-signature (multisig) approval process. Public investigation summaries describe an attack that did not “break” cold storage directly—instead, it compromised or deceived the signing/approval workflow so authorized signers approved something different than what they believed they were approving (Sygnia, 2025; NCC Group, 2025).
Days later, the U.S. FBI publicly attributed the theft to North Korea, referring to the activity as “TraderTraitor,” and urged virtual asset ecosystem entities to help disrupt laundering activity (Federal Bureau of Investigation, 2025).
Why you should care (even if you don’t touch crypto): This is a clean, modern example of a broader pattern—high-value approvals are a privileged workflow. If your organization relies on third-party control planes (SaaS consoles, signing portals, vendor-managed interfaces), your “offline” or “segregated” control is only as strong as the interface and verification path your approvers trust.
Bottom line lesson: Treat the highest-risk transactions/changes like privileged operations—independent verification, hardened approver devices, vendor control-plane governance, and auditable evidence capture.
Field Notes Opening
A cold wallet is supposed to feel like a vault: heavy door, thick steel, everything quiet.
But the Bybit case is a reminder that the quiet part isn’t the vault—it’s the moment right before the vault moves. If your signers can be shown a “safe-looking” request while the underlying action is different, the vault didn’t fail. The workflow did.
And in the real world of DoD/Federal supply chains, this isn’t a crypto-only problem. It’s the same failure mode as: - approving a “normal” vendor update that swaps a dependency, - accepting a “routine” configuration change that alters a control plane, - authorizing a “standard” transfer that reroutes value.
What We Know (Verified Facts)
Verified / broadly reported:
The theft was detected on or about February 21, 2025, and was reported as approximately $1.5B in virtual assets tied to an Ethereum cold wallet workflow (Federal Bureau of Investigation, 2025; Sygnia, 2025; AP News, 2025).
Public investigation summaries describe deception/compromise in the transaction approval workflow, where authorized signers were induced to approve a manipulated transaction (Sygnia, 2025; NCC Group, 2025).
The FBI publicly attributed the theft to North Korea (“TraderTraitor”) and warned the assets were being dispersed and laundered across blockchain addresses (Federal Bureau of Investigation, 2025).
Working technical narrative (reported by investigators)
Sygnia’s published summary ties the incident to compromise activity affecting Safe{Wallet} web interface infrastructure, followed by transaction manipulation at the moment of approval, with rapid cleanup of the malicious change after the theft (Sygnia, 2025).
NCC Group’s analysis reinforces the “approval process deception” theme: the attackers targeted the interface/approval layer rather than defeating multisig as a concept (NCC Group, 2025).
What We Don’t Know Yet (Unverified / Evolving)
Open questions that may shift as final reports mature:
Full scope: Whether related tooling, environments, or other organizations were impacted in similar ways (beyond what’s publicly disclosed).
Complete initial access chain: Public summaries describe a multi-stage compromise leading to interface manipulation, but organizations should assume details can evolve with additional forensics.
Defensive detection opportunities: Which detections (if any) could have flagged the workflow deception earlier, and what telemetry is “good enough” for high-value approvals.
Working assumption for this article:
We treat publicly released summaries (FBI PSA; Sygnia and NCC analysis) as sufficient for doctrine translation, while avoiding tactical details that would enable misuse.
Timeline (Simple)
Feb 21, 2025: Incident reported as detected/occurring “on or about” this date; theft of approximately $1.5B in virtual assets (Federal Bureau of Investigation, 2025; Sygnia, 2025).
Feb 26, 2025: FBI IC3 issues PSA attributing the theft to North Korea (“TraderTraitor”) and encourages ecosystem blocking of associated laundering activity (Federal Bureau of Investigation, 2025).
Mar 10, 2025: NCC Group publishes a technical analysis emphasizing workflow deception through the signing interface (NCC Group, 2025).
Mar 16, 2025: Sygnia publishes a consolidated investigation summary with a high-level attack timeline and findings (Sygnia, 2025).
Why This Matters (So What?)
For DoD/Federal supply chain practitioners, the Bybit incident is a “clean-room” lesson in modern control-plane risk:
Your control strength is defined at the point of decision If the approver’s view can be manipulated (UI, workflow routing, authorization context), then “strong back-end controls” are operating on bad intent.
Third-party control planes are part of your attack surface Modern security and operations rely on vendor-managed consoles and portals. If that interface is compromised, your internal approvals can be turned against you.
This pattern maps directly to mission/continuity risk In supply chains, the high-value workflow might be:
authorizing a firmware update,
approving a cloud policy change,
releasing funds/materials,
promoting code to production,
granting remote access to a vendor.
Treat these like “high consequence operations.” The point is not paranoia—it’s disciplined verification and evidence capture.
SEM Doctrine Translation
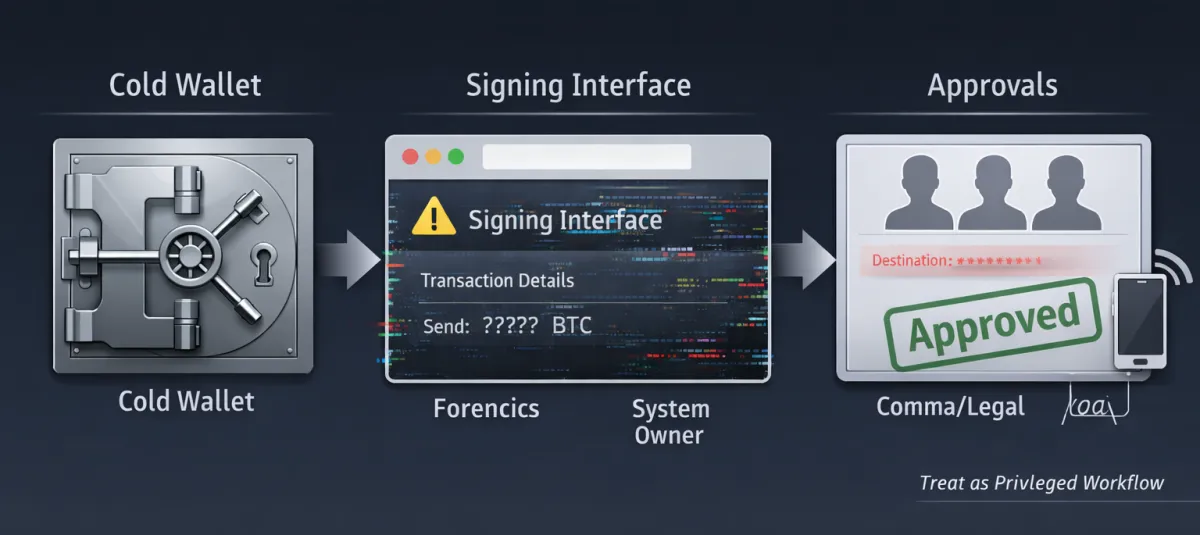
Doctrine concept: High-value approvals are privileged access.
Whether you’re moving money, pushing code, changing configurations, or authorizing vendor actions—the approval workflow is a control in itself, and it deserves privileged workflow protections.
How this maps to standard control families:
Access Control + least privilege: Approvals should be role-limited, task-bounded, and time-bounded—not “whoever has the token today.” (NIST SP 800-53 Rev. 5, 2020)
Configuration management + change control: Your approval interface and the policy logic it depends on should be version-controlled, monitored, and protected against unauthorized modification. (NIST SP 800-53 Rev. 5, 2020)
Supply chain risk management: Vendor-hosted interfaces and control planes need C-SCRM requirements, audit rights, incident notification SLAs, and monitoring/assurance expectations. (NIST SP 800-161 Rev. 1, 2022)
Continuous monitoring: High-value workflows warrant higher fidelity telemetry, alerting, and rapid forensics readiness. (NIST SP 800-137, 2011)
Doctrine translation (practitioner terms)
If you have any workflow where a small set of people can authorize a high-impact action, treat it like a privileged operation:
Independent verification (out-of-band): The approver must verify key fields through a second channel or second interface.
Harden the approver endpoint: Approver devices are “control-plane endpoints.” They must be locked down, monitored, and treated as high value.
Split trust: Where feasible, ensure no single vendor interface is the only “source of truth” for what’s being approved.
Evidence capture: For high-value actions, capture immutable “what was requested + what was approved + who approved + what actually executed.”

Figure 1 - “High-Value Approval Workflow: Trust Boundaries & Verification Points” [Aaron Gilmore] {Diagram showing a high-value request flowing through a signing interface to an approver decision and execution, with a highlighted risk zone at the interface and callouts for out-of-band verification and immutable logging.}
Lessons Learned (What this incident teaches)
Lesson 1: “Cold” controls can still fail at the human/interface layer If signers approve a manipulated request, the asset’s storage posture is irrelevant—what matters is the trustworthiness of the approval path (Sygnia, 2025; NCC Group, 2025).
Lesson 2: Third-party risk includes the control plane, not just the data plane Organizations often evaluate vendors on confidentiality and availability, but not on “what happens if the control console lies.” C-SCRM must include control-plane compromise scenarios (NIST SP 800-161 Rev. 1, 2022).
Lesson 3: Evidence capture is a control For high-value actions, the ability to prove what was requested/approved/executed is a defensive capability—technical containment and credibility move together.
Role-Based Implications (Who should do what)
Security leadership (CISO/CIO/Director):
Identify your top 3–5 “high-consequence approvals” (money, code, configuration, vendor access) and declare them privileged workflows.
Mandate independent verification and evidence capture for those workflows.
Security engineering / IAM / Zero Trust teams
Treat approver endpoints as Tier-0 assets: enforce hardened builds, EDR, phishing-resistant MFA, and strict browsing/app controls.
Implement “two-person integrity” patterns where feasible, and ensure logs are tamper-resistant.
Program management / compliance / ISSO/ISSM (DoD/Fed)
Translate privileged approval workflows into control language and assessment evidence (who approves, what is verified, what logs exist).
Ensure your SSP/POA&M includes control-plane vendor dependencies (not just internal systems).
Contracting / vendor risk / supply chain
Add C-SCRM clauses for control-plane vendors: audit/assurance, incident notification SLAs, integrity monitoring expectations, and subcontractor visibility. (NIST SP 800-161 Rev. 1, 2022)
IR / SOC
Pre-stage playbooks for “approval workflow deception”: preserve endpoint/browser evidence, validate “what executed” vs “what was shown,” and coordinate with vendor IR.
Legal / comms / public affairs
Pre-write a first-24-hour statement template that acknowledges impact, sets expectations, and commits to transparency without speculating.
What To Do Now (Field Application)
A. This week (60–90 minutes): find your “Bybit-like” workflow
1) List workflows where a small number of people approve a high-impact action.
2) For each workflow, answer: - What interface do approvers trust (console, portal, email link, signing tool)?
Is there an independent verification step (second channel / second source)?
What evidence is captured and where is it stored (tamper-resistant)?
3) Pick ONE workflow and harden it first.
B. Minimum viable hardening checklist (start here)
Out-of-band verification for key fields (destination, scope, identity, amount/change, timing).
Approver endpoint hardening (dedicated browser profile, allowlists, restricted extensions, EDR, phishing-resistant MFA).
Vendor control-plane governance (C-SCRM requirements, monitoring, escalation paths, incident SLAs).
Immutable logging + alerting on high-value approvals.
C. If you suspect an approval workflow deception event (first 4 hours)
Stop the workflow (pause high-value approvals/transfers/changes) until integrity is confirmed. - Preserve evidence: approver endpoint telemetry, browser cache/history as appropriate, approval logs, and vendor logs.
Validate outcomes: compare “what was executed” vs “what was displayed/approved” using an independent data source.
Coordinate with legal/comms early; avoid speculation; publish verified updates.

Figure 2- “First 4 Hours: Approval Deception Response Loop (Contain → Preserve → Validate → Communicate)” [Aaron Gilmore] {Loop diagram showing four steps—contain, preserve evidence, validate outcome, communicate verified facts—with small role labels under each step.}
Note from the Author
Industrial security is full of “strong doors” that fail because the key got copied, the guard got distracted, or the checklist became a formality. The Bybit incident is the cyber version of that lesson. If your organization has any approval that can move money, change safety posture, release sensitive designs, or grant vendor access—treat that approval like a privileged operation. Don’t trust one interface. Verify. Capture evidence. Drill it. Do it!!!
Reference List
AP News. (2025, February 22). Cryptocurrency exchange says it was victim of $1.5 billion hack. Associated Press. https://apnews.com/article/88256366c723a9de8327ef3d4071057e
Federal Bureau of Investigation. (2025, February 26). North Korea responsible for $1.5 billion Bybit hack (Alert Number: I-022625-PSA). Internet Crime Complaint Center (IC3). https://www.ic3.gov/PSA/2025/PSA250226
National Institute of Standards and Technology. (2011, September). Information security continuous monitoring (ISCM) for federal information systems and organizations (NIST SP 800-137). https://csrc.nist.gov/pubs/sp/800/137/final
National Institute of Standards and Technology. (2020, September). Security and privacy controls for information systems and organizations (NIST SP 800-53 Rev. 5). https://csrc.nist.gov/pubs/sp/800/53/r5/upd1/final
National Institute of Standards and Technology. (2022, May). Cybersecurity supply chain risk management practices for systems and organizations (NIST SP 800-161 Rev. 1). https://csrc.nist.gov/pubs/sp/800/161/r1/final
NCC Group. (2025, March 10). In-depth technical analysis of the Bybit hack. NCC Group Research Blog. https://www.nccgroup.com/research-blog/in-depth-technical-analysis-of-the-bybit-hack/
Sygnia. (2025, March 16). Bybit – What we know so far. Sygnia Blog. https://www.sygnia.co/blog/sygnia-investigation-bybit-hack/