Beware the Sandworm: Shai‑Hulud and the New Shape of Package‑Manager Worms
Shai‑Hulud and Sha1‑Hulud 2.0 show how npm worms spread via stolen tokens. Learn how to lock publishing, harden CI, and rotate secrets fast.

Shai‑Hulud and Sha1‑Hulud 2.0 show how npm worms spread via stolen tokens. Learn how to lock publishing, harden CI, and rotate secrets fast.
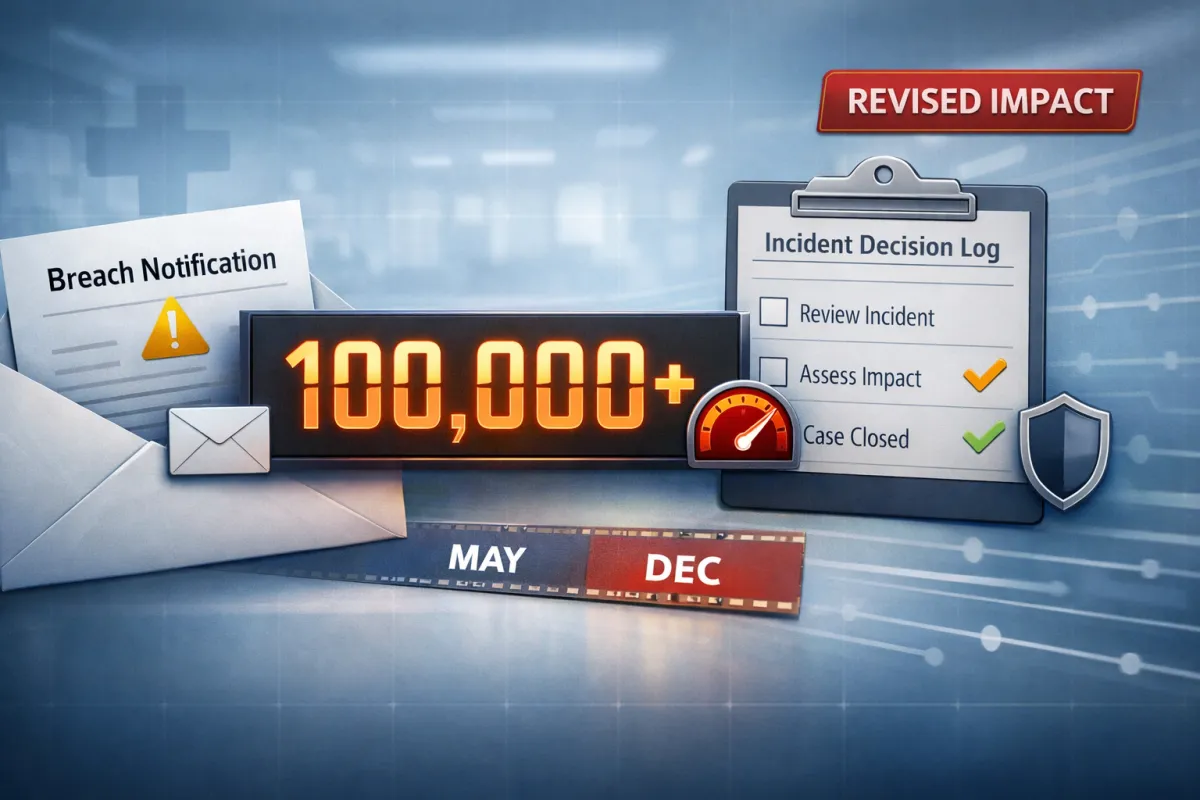
When breach impact gets revised upward, the cost isn’t just records—it’s trust, governance, notification waves, and long-tail recovery work. Lessons from Covenant Health.

JLR’s 2025 cyber disruption shows how IT outages become supply-chain failures. Protect ERP/MES/identity, test IT/OT segmentation, and plan fallback operations.
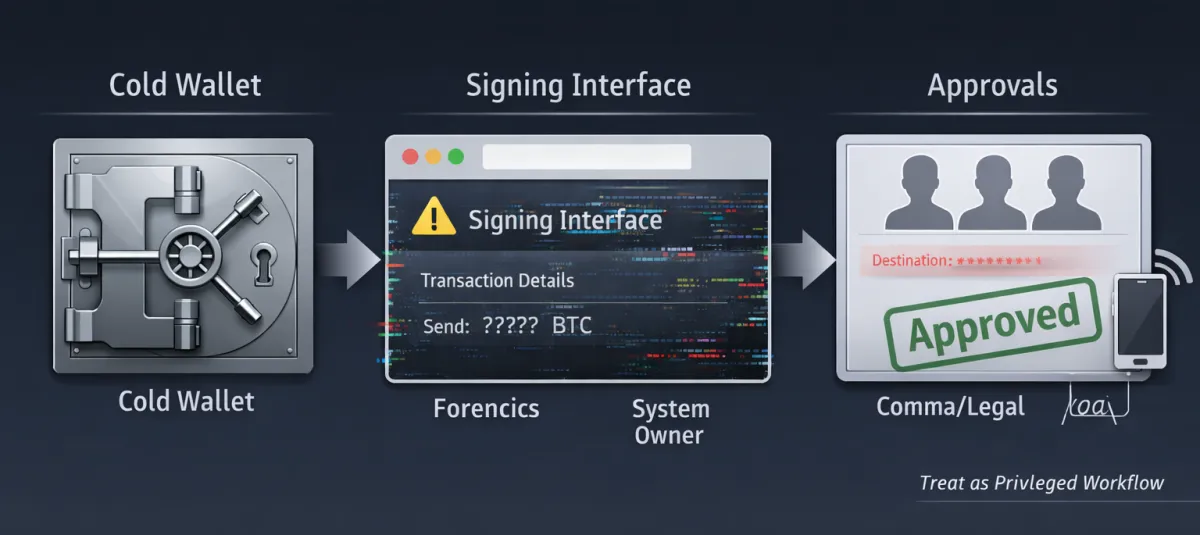
The Bybit theft shows “cold storage” fails when signing/approval workflows are deceived. Lessons for privileged approvals, vendor risk, and comms.
AI tools assist with research, ideation, and content organization on this blog. All posts are reviewed and approved by our cybersecurity team before publication. Our goal is to provide accurate, actionable insights informed by real-world experience.
This content is for informational purposes only and does not constitute professional cybersecurity, legal, or compliance advice.
© 2026 BEES COMPUTING. All rights reserved.
Designed & Developed by KATALYST CRM