Covenant Health Ransomware: The Real Cost of Revised Impact
When the numbers change months later, the real cost shows up in governance, trust, and the second wave of recovery work.
By: Aaron Gilmore — Intergalactic SEM Consultant (humans only so far).
Human-led, Automation Enhanced. SEM-Artificium
QuickScan
“Revised impact” means the scope changed after deeper forensics—usually months after initial disruption.
The second wave is expensive: new notification mailings, expanded call-center load, renewed media attention, and more victim-support services.
The operational failure isn’t always the intrusion—it’s weak data mapping and weak decision logging that make scope discovery slow.
Good programs plan for scope expansion: “notification waves,” predefined thresholds, and a closure tracker for corrective actions.
Trust recovery is a control: consistent messaging + evidence of improvements (not just apologies).
For Who
Primary audience: DoD/Federal Supply Chain
Also useful for: Healthcare & critical services, privacy/compliance teams, cyber IR leaders, vendor management, and security governance boards.
What You’ll Get
You will learn: Why breach scope often expands after the first report and how that triggers new legal/operational obligations.
You will be able to do: Build a “Scope Expansion Playbook” that includes decision triggers, comms scripts, and a recommendation-to-closure tracker.
Time & Effort Read time: 8–9 minutes
Do time (optional): 30–60 minutes
Difficulty: Intermediate
The breach didn’t change—your understanding of it did.
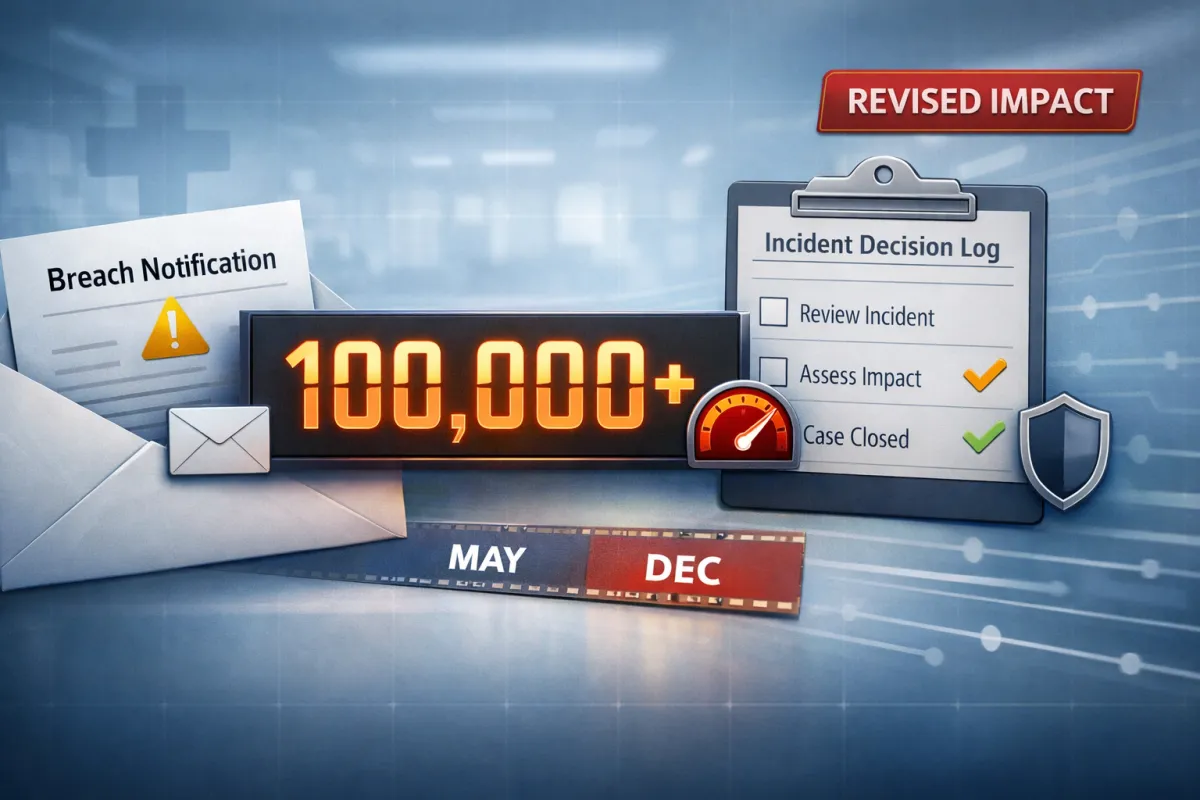
Executive Snapshot
What happened: Covenant Health reported unusual activity in its IT environment on May 26, 2025 and later stated that an unauthorized party accessed certain systems between May 18 and May 26, 2025. Notification letters began mailing on July 11, 2025, and a second notification wave began on December 31, 2025 after ongoing review expanded the affected population. (Covenant Health, n.d.; Maine Attorney General, n.d.)
What changed: Public filings show the affected count ultimately reported as 478,188 total individuals, including 284,529 Maine residents—far above early public figures reported in mid-2025. (Maine Attorney General, n.d.; Fox, 2026; Ilascu, 2026)
Why it matters: “Revised impact” is a governance stress test. It expands legal notification workload, increases victim-support obligations, reopens reputational damage, and signals gaps in data mapping and impact analysis that can exist in any enterprise—especially those relying on third-party forensics and complex data environments. (HHS, n.d.; NIST, 2012)
What to do now:
Build an “Impact Analysis Cell” as a formal incident workstream with deadlines, confidence levels, and a decision log (so scope can expand without chaos). (NIST, 2012)
Plan for notification waves: pre-approved comms scripts, surge capacity (mail/call center), and clear criteria for when counts will be updated. (HHS, n.d.)
Treat trust recovery as an operational deliverable: publish concrete control improvements and track them to verified closure. (NIST, 2024)
Key lesson: The breach didn’t change—your understanding of the breach did—and mature programs are built to handle that change without losing control of governance, communications, and victim support.
Field Notes Opening
A second envelope arrives months later. Not the first letter. Not the “we had an incident” letter. The follow-on letter:
“Through ongoing analysis, we determined your information may have been involved.”
That’s what “revised impact” sounds like in the real world. It’s not only a number. It’s a second wave of labor, scrutiny, and downstream harm you now have to manage.
What We Know (Verified Facts)
Confirmed facts from public notices, filings, and reputable reporting:
Covenant Health stated it detected unusual activity on May 26, 2025 and identified an unauthorized access window of May 18–May 26, 2025. (Covenant Health, n.d.; Maine Attorney General, n.d.)
Covenant Health began mailing notification letters on July 11, 2025 and stated it may mail additional letters if more individuals are identified through ongoing review. (Covenant Health, n.d.)
Maine’s breach portal entry lists written notifications on 07/11/2025 and 12/31/2025 and reports 478,188 total affected individuals and 284,529 Maine residents affected; it also notes identity monitoring services offered (12 months, Experian). (Maine Attorney General, n.d.)
Public reporting in early January 2026 highlighted the sharp increase from early figures (e.g., 7,864 initially reported in some coverage) to nearly 478,000. (Fox, 2026; Ilascu, 2026)
Potentially involved information (varies by individual) may include names and one or more of: address, date of birth, medical record number, Social Security number, and treatment/insurance information. (Covenant Health, n.d.)
Adversary claims and/or ransomware-group attribution have been reported by cybersecurity news outlets; treat these as claims unless confirmed by official statements or law enforcement. (Ilascu, 2026)
Field note: You can extract solid doctrine from these verified facts without a complete adversary narrative.
What We Don’t Know Yet (Unverified / Evolving)
These are normal unknowns at this stage and are often the reason “impact” keeps changing:
Exact initial access vector (phishing/credentials, vulnerability exploitation, vendor pathway, etc.).
Whether data were exfiltrated, merely accessed, or both—at a per-record level.
What “ongoing review” methodology expanded the scope (log correlation, data-store discovery, forensic tool coverage changes, etc.).
Any extortion/payment details (not confirmed in primary notices).
Why that’s okay for this lesson: This article is about the mechanism of scope expansion and second-wave response—not assigning blame.
Timeline
May 18, 2025 — Start of unauthorized access window (per public filing). (Maine Attorney General, n.d.)
May 26, 2025 — Unusual activity detected / incident discovery (per public filing). (Maine Attorney General, n.d.)
July 11, 2025 — First notification wave begins. (Covenant Health, n.d.; Maine Attorney General, n.d.)
Dec 31, 2025 — Second notification wave begins (expanded scope). (Maine Attorney General, n.d.)
Jan 2–5, 2026 — Major outlets report “revised impact” and the expanded patient count. (Ilascu, 2026; Fox, 2026)

Figure 1 - "Covenant Health — Notification Waves & Scope Expansion Timeline (May 2025–Jan 2026)" [Aaron Gilmore] {Timeline showing the reported May 2025 access window and discovery date, the July 2025 first notification wave, the December 31, 2025 second notification wave, and January 2026 reporting on the revised impacted count.}
Why This Matters (So What?)
“Revised impact” is the cost you pay when your first impact estimate is not tied to a mature data map and a disciplined analysis process.
What “revised impact” usually means operationally:
Your understanding of which systems/data stores were affected expanded.
Your ability to link identities to affected records improved.
Your confidence threshold changed (e.g., from “confirmed” to “reasonably believed”). (HHS, n.d.; 45 CFR § 164.404)
Why it hits hard (second-wave costs):
A second mail campaign (print, verify addresses, track returns)
A second call-center surge and renewed stakeholder concerns
Expanded victim-support services and internal case handling
Renewed regulator/partner scrutiny
Reputational damage that reactivates when the story returns to the news cycle
DoD/Federal supply chain implication: If you provide services to government or rely on partners who do, the real risk isn’t just “a breach happened.” It’s “governance and trust now become variables,” which can affect access, contracts, mission timelines, and oversight requirements.
SEM Doctrine Translation
This incident maps cleanly to three doctrine blocks that travel well across sectors:
Impact analysis as a managed workstream (not a side-task)
Notification readiness (waves, triggers, and evidence)
Governance follow-through (decision logging + corrective action closure)
Impact analysis must be staffed like a function
NIST incident handling guidance emphasizes analysis as a core activity—organizations must examine data sources and determine appropriate response actions. (NIST, 2012)
Practical doctrine
Create an “Impact Analysis Cell” with:
A single accountable owner
A defined confidence scale (Confirmed / Likely / Possible)
A list of authoritative data sources (logs, system inventories, backups, EHR systems, file shares, identity stores)
A daily/weekly update cadence to leadership
A decision log for when scope changes and why
Plan for notification waves (don’t treat them as failure)
Healthcare breach notification rules require notification following discovery of a breach of unsecured protected health information; organizations also often face state-specific notification requirements. (HHS, n.d.; 45 CFR § 164.404)
Doctrine takeaway:
Treat notification as a phased operation with “waves” (Wave 1 = best-known scope; Wave 2 = expanded scope if identified).
Predefine triggers for re-notification (new data store discovered, new identity linkage, new confidence threshold reached).
Pre-stage surge capacity: mail vendor, call center, FAQs, and scripts.
Decision logging is your credibility layer
Your credibility is not created by “we take privacy seriously.” It’s created by:
what you decided
when you decided it
what evidence you used
and what you changed afterward
This is governance: converting findings into actions and tracking them to verified closure. (NIST, 2024; NIST, 2012)

Figure 2 - "Scope Expansion Pipeline (Impact Analysis → Notification Waves → Closure)" [Aaron Gilmore] {Flow diagram showing an impact analysis workstream producing confidence levels and decision gates that trigger one or more notification waves, supported by victim-support operations and tracked corrective actions to verified closure.}
Lessons Learned
Your first impacted count is rarely your final one—say that early and build expectations.
Scope expansion is normal; unplanned scope expansion is costly.
Treat impact analysis as a staffed cell with deadlines, not a background task.
“Second-wave” operations (mail + call center + monitoring) should be pre-negotiated, not improvised.
Decision logs protect trust: they show disciplined governance under uncertainty.
Corrective actions must close with evidence—or you’ll relive the same incident later.
Role-Based Implications (Who should do what)
Leadership / Executives
Ask for the Scope Expansion Playbook: triggers, budgets, and who owns wave decisions.
Require two dashboards: (1) patient/consumer impact confidence, (2) corrective action closure progress.
Security / IR leadership
Stand up the Impact Analysis Cell with inventory access and authority.
Track “coverage gaps” in forensics (systems not yet analyzed) as a primary risk.
Privacy / Compliance / Legal
Align the “reasonably believed” threshold with documented rationale and consistent language.
Validate notification content and maintain consistency across waves.
Public Affairs / Communications
Use one narrative: what we know, what we don’t, what’s changing, and what victims should do now.
Prepare for wave #2 as a likely event; don’t treat it as a surprise.
Vendor / Third-Party Management
Confirm forensic vendor scope, deliverables, and evidence requirements.
Ensure vendors can support surge needs (mail, call center, identity monitoring) without delays.
Continuity / Resilience (BCP)
Treat long-tail recovery as part of the incident (not “post-incident”): staffing, funding, fatigue management.
What To Do Now (Field Application)
Build a “Scope Expansion Playbook” in 60 minutes
Owner: name the person who owns scope decisions.
Confidence scale: Confirmed / Likely / Possible.
Update cadence: daily internal; weekly external (or as required).
Notification wave triggers: list 5 triggers (new data store, new identity linkage, new forensic coverage, new legal threshold, new third-party discovery).
Minimum fields for an Impact/Notification Decision Log
Decision ID
Date/time
Evidence summary (what changed)
Confidence level
Scope delta (counts, populations)
Legal basis / threshold (“reasonably believed”)
Messaging changes (what victims should do)
Approver(s)

Figure 3 - "Decision Log + Closure Tracker (Minimum Schema)" [Aaron Gilmore] {Two table-style templates: one for logging scope/notification decisions with evidence and confidence, and one for tracking corrective actions to verified closure with required evidence.}
Victim guidance (keep it operational)
Include plain, actionable steps and point to official resources for identity theft recovery (FTC, n.d.). Take immediate action to repair the damage done, create easy to understand milestones for how you are repairing the damage to you customers and communicate your action plan to restore customer confidence.
Note from the Author
“Revised impact” isn’t just a number. It’s the moment your organization discovers whether it can govern uncertainty. Build the cell, Log the decisions, Close the actions. No matter if you dropped the ball or you did everything right, the moment you lie to the public about these type of events, you cause brand damage and confidence from the public (customers and government bodies alike). When you withhold information it causes damage as well, but as you will learn or know, withholding information is not the same as lying about information. OPSEC, or Operational Security, does require leadership to keep the "need to know" information to a limited amount of individuals to prevent leaks and to prevent gossip that takes the concept of the "telephone game" and injects it with steroids. These type of events require a very careful balance of being transparent without fully disclosing information that will create further damage to customers, employees and the data your protecting. Cybercrime isn't going way any time soon, and orgs continue to place cybersecurity on the back burner (NOT to infer that is what happened in this ransomware case at all). Make sure your org realizes the risks when you hold data in information systems and responds accordingly, so you don't end up as a firm that is "breached" OR a firm that was "breached due to negligence". Incidents happen, but if the fault lies with you it can become a career ending moment or a potential death of your company. Getting breached because "the enemy found a vulnerability", is way different then being breached because "you knowingly allowed yourself to be vulnerable". And if you have caught on to a repeating trend in these breach articles, if you think your safe from a malicious attack....your not.
Reference List
Covenant Health. (n.d.). Cybersecurity. Retrieved January 18, 2026, from https://covenanthealth.net/cybersecurity/
Federal Trade Commission. (n.d.). Report identity theft. Retrieved January 18, 2026, from https://www.ftc.gov/news-events/topics/identity-theft/report-identity-theft
Fox, A. (2026, January 5). Covenant Health patient data breach numbers skyrocket. Healthcare IT News. https://www.healthcareitnews.com/news/covenant-health-patient-data-breach-numbers-skyrocket
Ilascu, I. (2026, January 2). Covenant Health says May data breach impacted nearly 478,000 patients. BleepingComputer. https://www.bleepingcomputer.com/news/security/covenant-health-says-may-data-breach-impacted-nearly-478-000-patients/
National Institute of Standards and Technology. (2012). Computer security incident handling guide (SP 800-61 Rev. 2). https://csrc.nist.gov/pubs/sp/800/61/r2/final
National Institute of Standards and Technology. (2024). The NIST Cybersecurity Framework (CSF) 2.0 (CSWP 29). https://csrc.nist.gov/pubs/cswp/29/the-nist-cybersecurity-framework-csf-20/final
Office for Civil Rights, U.S. Department of Health & Human Services. (n.d.). Breach Notification Rule. Retrieved January 18, 2026, from https://www.hhs.gov/hipaa/for-professionals/breach-notification/index.html
Office of the Maine Attorney General. (n.d.). Breach information portal entry: Covenant Health, Inc. Retrieved January 18, 2026, from https://www.maine.gov/agviewer/content/ag/985235c7-cb95-4be2-8792-a1252b4f8318/2637476a-ce93-46b9-a8c9-e2705955dc98.html
eCFR. (n.d.). 45 CFR § 164.404 — Notification to individuals. Retrieved January 18, 2026, from https://www.ecfr.gov/current/title-45/subtitle-A/subchapter-C/part-164/subpart-D/section-164.404